 Probably the most overlooked aspect of managing your website is the fact that it needs to be secured on an ongoing basis. In this article we will cover what things need to be done as the beginnings of your security policy. A later article will cover more advanced topics such as content security policies, security headers and the like.
Probably the most overlooked aspect of managing your website is the fact that it needs to be secured on an ongoing basis. In this article we will cover what things need to be done as the beginnings of your security policy. A later article will cover more advanced topics such as content security policies, security headers and the like.
With security it is best to defend in depth. Defending in depth means that there are a number of barriers to overcome before access can be gained to a resource. This approach is to be chosen in preference to security through obscurity where you rely on hiding something to make it more secure.
The steps defined below are there to make it hard and frustrating for an attacker to get into your site, so that they will give up and go for easier pickings.
Step 1: Choose Strong Passwords For All User Accounts
For any content management system [CMS] used, where to access the administrator access for the website are well know. For WordPress this is wp-admin eg. www.mywordpressite.com.au/wp-admin, for Joomla! this is administrator www.myjoomlawebsite.com.au/administrator.
A hacker is then free to try various password combinations to see if they can access the site. Stay away from common usernames such as administrator, admin, root, editor etc.
It is also best to use a password that contains letters, numbers, punctuation and the longer the better. So something like
A-*V>qtfmhus7Q/-
(APPLE - * VISA > queen tokyo fruit music hulu usa skype 7 QUEEN / -) is better than your pet's name.
Step 2: Obfusticate Access To The Administrator Access
If an attacker cannot find the administrator url they will be unable to get to the login form for the back end.
This can either take the form of changing the url in its entirety so instead of www.myjoomlawebsite.com.au/administrator we change it to www.myjoomlawebsite.com.au/orange or any other random string in place of orange or we add something extra to the URL to allow the password form to be displayed such as www.myjoomlawebsite.com.au/administrator?G0bL1n! where unless ?G0bLin! is entered the login form is not displayed and the user is redirected to the home page.
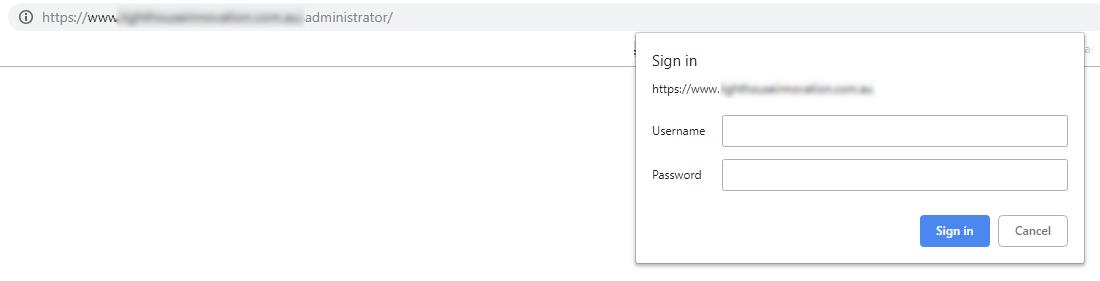
Step 3: Add Basic Authentication Protection To The Administrator Access
Here we add an additional layer of security requiring the user to enter a username and password before they can access anything associated with the administration back end.
In the example below the user is being prompted because they are accessing the www.myjoomlawebsite.com.au/administrator for a Joomla! website.
Step 4: Add Web Application Firewall
This is a piece of software that is added to the CMS to monitor all activities within the CMS. Whether it be a user logging in, content being changed, security permissions being changed or any other activities within the CMS. Alert thresholds can then be set so that administrators and site maintainers are notified when activities take place.
Step 5: Keep Up With Updates & Security Updates to the CMS
This step is extremely crucial and probably the one least followed by site owners. The CMS software is not perfect and often security issues are identified and fixed. These fixes are then made available as a new version of the CMS. It is important to keep updating the CMS so that your site remains as secure as can be.
It’s important to remember that managing a website means being able to manage both the content and some basic technical tasks. This can save you both time and money and will give you the flexibility to accommodate growth and changing requirements.
Our 6-part workshop series titled “Managing your Website after Launch” doesn't require any programming knowledge and covers post-launch tasks, UX design, testing and more. https://www.eventbrite.com.au/e/managing-your-website-after-launch-tickets-53378996014 
About Natiki
Managing a website is more than just uploading content. The team at Natiki Web Solutions helps to demystify some of the jargon for small business owners and non-techies.


